
This tutorial walks you through the steps to set up a complete web hosting solution on an Debian 9 server with ISPConfig 3.
The web hosting control panel ISPConfig 3 allows you to configure the following services through a web browser: Apache or nginx web server, Postfix mail server, Courier or Dovecot IMAP/POP3 server, MySQL, BIND or MyDNS nameserver, PureFTPd, SpamAssassin, ClamAV, and lots more.
In this tutorial, we will use the hostname labserver.example.com with the IP address 192.168.1.100 and the gateway 192.168.1.1. Before proceeding this guide, you need to have a minimal installation of Debian 9.
Install the OpenSSH server
If you did not install the OpenSSH server during the system installation, you can install it now by running the following:apt-get install ssh openssh-server
Now you can use an SSH client such as PuTTY and connect from your workstation to your Debian 9 server and follow the remaining steps from this guide.
Configure the Hostname
The hostname of your server should be a subdomain like "labserver.example.com". Do not use a domain name without subdomain part like "example.com" as hostname as this will cause problems later with your mail setup. First, you should check the hostname in /etc/hosts and change it when necessary. The line should be: "IP Address - space - full hostname incl. domain - space - subdomain part". For our hostname labserver.example.com, the file should look like this:
127.0.0.1 localhost.localdomain localhost
192.168.1.100 labserver.example.comlabserver
Then edit the /etc/hostname file:
nano /etc/hostname
It should contain only the hostname without domain.name
labserver
Save and close
Finally, reboot the server to apply the change:
reboot
Log in again and check if the hostname is correct now with these commands:
hostname
hostname -f
Update Debian Installation
First, make sure that your /etc/apt/sources.list contains the stretch/updates repository (this makes sure you always get the newest security updates), and that the contrib and non-free repositories are enabled as some required packages are not in the main repository.nano /etc/apt/sources.list
deb http://ftp.us.debian.org/debian/ stretch main contrib non-free
deb-src http://ftp.us.debian.org/debian/ stretch main contrib non-free
deb http://security.debian.org/debian-security stretch/updates main contrib non-free
deb-src http://security.debian.org/debian-security stretch/updates main contrib non-free
Save and close
Now run the following to update the apt package database:
apt-get update
apt-get upgrade
Change the default Shell
/bin/sh is a symlink to /bin/dash, however we need /bin/bash, not /bin/dash. Therefore we do this:dpkg-reconfigure dash
Use dash as the default system shell (/bin/sh)? no
If you don't do this, the ISPConfig installation will fail.
Install Postfix, Dovecot, MySQL, rkhunter, and Binutils
We can install Postfix, Dovecot, MySQL, rkhunter, and Binutils with a single command:apt-get install postfix postfix-mysql postfix-doc mariadb-client mariadb-server openssl getmail4 rkhunter binutils dovecot-imapd dovecot-pop3d dovecot-mysql dovecot-sieve dovecot-lmtpd sudo
When you prefer MySQL over MariaDB, replace the packages "mariadb-client mariadb-server" in the above command with "mysql-client mysql-server".
You will be asked the following questions:
General type of mail configuration: example.com
System mail name: labserver.example.com
To secure the MariaDB / MySQL installation and to disable the test database, run this command:
mysql_secure_installation
Answer the questions as follows:
Change the root password? [Y/n] y
New password:******
Re-enter new password: ******
Remove anonymous users? [Y/n] y
Disallow root login remotely? [Y/n] y
Remove test database and access to it? [Y/n] y
Reload privilege tables now? [Y/n] y
Next, open the TLS/SSL and submission ports in Postfix:
nano /etc/postfix/master.cf
Uncomment the submission and smtps sections as follows and add lines where necessary so that this section of the master.cf file looks exactly like the one below.
submission inet n - - - - smtpd
-o syslog_name=postfix/submission
-o smtpd_tls_security_level=encrypt
-o smtpd_sasl_auth_enable=yes
-o smtpd_client_restrictions=permit_sasl_authenticated,reject
# -o smtpd_reject_unlisted_recipient=no
# -o smtpd_client_restrictions=$mua_client_restrictions
# -o smtpd_helo_restrictions=$mua_helo_restrictions
# -o smtpd_sender_restrictions=$mua_sender_restrictions
# -o smtpd_recipient_restrictions=
# -o smtpd_relay_restrictions=permit_sasl_authenticated,reject
# -o milter_macro_daemon_name=ORIGINATING
smtps inet n - - - - smtpd
-o syslog_name=postfix/smtps
-o smtpd_tls_wrappermode=yes
-o smtpd_sasl_auth_enable=yes
-o smtpd_client_restrictions=permit_sasl_authenticated,reject
# -o smtpd_reject_unlisted_recipient=no
# -o smtpd_client_restrictions=$mua_client_restrictions
# -o smtpd_helo_restrictions=$mua_helo_restrictions
# -o smtpd_sender_restrictions=$mua_sender_restrictions
# -o smtpd_recipient_restrictions=
# -o smtpd_relay_restrictions=permit_sasl_authenticated,reject
# -o milter_macro_daemon_name=ORIGINATING
Now restart Postfix to take changes effect:
service postfix restart
We want MySQL to listen on all interfaces, not just localhost. Therefore, we edit /etc/mysql/mariadb.conf.d/50-server.cnf and comment out the line bind-address = 127.0.0.1 and add the line sql-mode="NO_ENGINE_SUBSTITUTION":
nano /etc/mysql/mariadb.conf.d/50-server.cnf
# Instead of skip-networking the default is now to listen only on
# localhost which is more compatible and is not less secure.
#bind-address = 127.0.0.1
sql-mode="NO_ENGINE_SUBSTITUTION"
Set the password authentication method in MariaDB to native so we can use PHPMyAdmin later to connect as root user:
echo "update mysql.user set plugin = 'mysql_native_password' where user='root';" | mysql -u root
Edit the file /etc/mysql/debian.cnf and set the MYSQL / MariaDB root password there twice in the rows that start with password.
nano /etc/mysql/debian.cnf
The MySQL root password that needs to be added is shown in red, in this example the password is "password".
# Automatically generated for Debian scripts. DO NOT TOUCH!
[client]
host = localhost
user = root
password = password
socket = /var/run/mysqld/mysqld.sock
[mysql_upgrade]
host = localhost
user = root
password = password
socket = /var/run/mysqld/mysqld.sock
basedir = /usr
Then restart MariaDB:
service mysql restart
Now check that networking is enabled. Run
netstat -tap | grep mysql
The output should look like this:
tcp6 0 0 [::]:mysql [::]:* LISTEN 17776/mysqld
Install Amavisd-new, SpamAssassin, and ClamAV
To install amavisd-new, SpamAssassin and ClamAV, we runapt-get install amavisd-new spamassassin clamav clamav-daemon zoo unzip bzip2 arj nomarch lzop cabextract apt-listchanges libnet-ldap-perl libauthen-sasl-perl clamav-docs daemon libio-string-perl libio-socket-ssl-perl libnet-ident-perl zip libnet-dns-perl libdbd-mysql-perl postgrey
The ISPConfig 3 setup uses amavisd which loads the SpamAssassin filter library internally, so we can stop SpamAssassin to free up some RAM:
service spamassassin stop
systemctl disable spamassassin
Install Metronome XMPP Server
This step installs the Metronome XMPP Server which provides a chat server that is compatible with the XMPP protocol. This step is optional, if you do not need a chat server, then you can skip this step. No other ISPConfig functions depend on this software.Add the Prosody package repository in Debian.
echo "deb http://packages.prosody.im/debian stretch main"> /etc/apt/sources.list.d/metronome.list
wget http://prosody.im/files/prosody-debian-packages.key -O - | sudo apt-key add -
Update the package list:
apt-get update
and install the packages with apt.
apt-get install git lua5.1 liblua5.1-0-dev lua-filesystem libidn11-dev libssl-dev lua-zlib lua-expat lua-event lua-bitop lua-socket lua-sec luarocks luarocks
luarocks install lpc
Add a shell user for Metronome.
adduser --no-create-home --disabled-login --gecos 'Metronome' metronome
Download Metronome to the /opt directory and compile it.
cd /opt; git clone https://github.com/maranda/metronome.git metronome
cd ./metronome; ./configure --ostype=debian --prefix=/usr
make
make install
Metronome has now be installed to /opt/metronome.
Install Apache2, PHP, FCGI, suExec, Pear, phpMyAdmin, and mcrypt
Apache2, PHP5, phpMyAdmin, FCGI, suExec, Pear, and mcrypt can be installed as follows:apt-get -y install apache2 apache2-doc apache2-utils libapache2-mod-php php7.0 php7.0-common php7.0-gd php7.0-mysql php7.0-imap phpmyadmin php7.0-cli php7.0-cgi libapache2-mod-fcgid apache2-suexec-pristine php-pear php7.0-mcrypt mcrypt imagemagick libruby libapache2-mod-python php7.0-curl php7.0-intl php7.0-pspell php7.0-recode php7.0-sqlite3 php7.0-tidy php7.0-xmlrpc php7.0-xsl memcached php-memcache php-imagick php-gettext php7.0-zip php7.0-mbstring memcached libapache2-mod-passenger php7.0-soap
You will see the following questions:
Web server to reconfigure automatically: apache2
Configure database for phpmyadmin with dbconfig-common? yes
Enter the phpmyadmin application password? Hit Enter
Enter the password of the administrative user? (rootmysqlpassword)
Then run the following command to enable the Apache modules suexec, rewrite, ssl, actions, and include (plus dav, dav_fs, and auth_digest if you want to use WebDAV):
a2enmod suexec rewrite ssl actions include dav_fs dav auth_digest cgi headers
To ensure that the server can not be attacked trough the HTTPOXY vulnerability, we will disable the HTTP_PROXY header in apache globally by adding the configuration file /etc/apache2/conf-available/httpoxy.conf.
nano /etc/apache2/conf-available/httpoxy.conf
Enter the following content to the file:
RequestHeader unset Proxy early
And enable the module by running:
a2enconf httpoxy
service apache2 restart
Install Let's Encrypt
ISPConfig 3.1 has support for the free SSL Certificate authority Let's encrypt. The Let's Encrypt function allows you to create free SSL certificates for your website from within ISPConfig.Now we will add support for Let's encrypt.
apt-get install certbot
There are no further steps required than installing LE. The website SSL certificates are created by ISPConfig when you add the web sites.
Install PHP-FPM
To use PHP-FPM with Apache, we need the mod_proxy_fcgi Apache module, which is installed by default and needs just be enabled. We can install PHP-FPM and as follows:apt-get -y install php7.0-fpm
Make sure you enable the modules and restart Apache:
a2enmod actions proxy_fcgi alias
service apache2 restart
Install PHP Opcode Cache
Opcache is a free PHP opcode cacher for caching and optimizing PHP intermediate code. APCu is a compatibility module which provides APC compatible functions for Opcache which is used by many CMS caching systems. It is recommended to have these PHP extensions installed to speed up your PHP page.APCu can be installed as follows:
apt-get -y install php7.0-opcache php-apcu
Now restart Apache:
service apache2 restart
Install Mailman
ISPConfig allows you to manage (create/modify/delete) Mailman mailing lists. If you want to make use of this feature, install Mailman as follows:apt-get install mailman
Select at least one language, e.g.:
Languages to support: en (English)
Missing site list: Ok
Before we can start Mailman, a first mailing list called mailman must be created:
newlist mailman
Enter the email of the person running the list: admin@example.com
Initial mailman password: ******
To finish creating your mailing list, you must edit your /etc/aliases (or
equivalent) file by adding the following lines, and possibly running the
`newaliases' program:
## mailman mailing list
mailman: "|/var/lib/mailman/mail/mailman post mailman"
mailman-admin: "|/var/lib/mailman/mail/mailman admin mailman"
mailman-bounces: "|/var/lib/mailman/mail/mailman bounces mailman"
mailman-confirm: "|/var/lib/mailman/mail/mailman confirm mailman"
mailman-join: "|/var/lib/mailman/mail/mailman join mailman"
mailman-leave: "|/var/lib/mailman/mail/mailman leave mailman"
mailman-owner: "|/var/lib/mailman/mail/mailman owner mailman"
mailman-request: "|/var/lib/mailman/mail/mailman request mailman"
mailman-subscribe: "|/var/lib/mailman/mail/mailman subscribe mailman"
mailman-unsubscribe: "|/var/lib/mailman/mail/mailman unsubscribe mailman"
Hit enter to notify mailman owner. ENTER
Now edit /etc/aliases file:
nano /etc/aliases
and add the following lines:
## mailman mailing list
mailman: "|/var/lib/mailman/mail/mailman post mailman"
mailman-admin: "|/var/lib/mailman/mail/mailman admin mailman"
mailman-bounces: "|/var/lib/mailman/mail/mailman bounces mailman"
mailman-confirm: "|/var/lib/mailman/mail/mailman confirm mailman"
mailman-join: "|/var/lib/mailman/mail/mailman join mailman"
mailman-leave: "|/var/lib/mailman/mail/mailman leave mailman"
mailman-owner: "|/var/lib/mailman/mail/mailman owner mailman"
mailman-request: "|/var/lib/mailman/mail/mailman request mailman"
mailman-subscribe: "|/var/lib/mailman/mail/mailman subscribe mailman"
mailman-unsubscribe: "|/var/lib/mailman/mail/mailman unsubscribe mailman"
Run the following command:
newaliases
and restart Postfix:
service postfix restart
Finally, we must enable the Mailman Apache configuration:
ln -s /etc/mailman/apache.conf /etc/apache2/conf-enabled/mailman.conf
This defines the alias /cgi-bin/mailman/ for all Apache vhosts, which means you can access the Mailman admin interface for a list at http://labserver.example.com/cgi-bin/mailman/admin/, and the web page for users of a mailing list can be found at http://labserver.example.com/cgi-bin/mailman/listinfo/.
Restart Apache afterwards:
service apache2 restart
Then start the Mailman daemon:
service mailman start
Install PureFTPd and Quota
PureFTPd and quota can be installed with the following command:apt-get install pure-ftpd-common pure-ftpd-mysql quota quotatool
Edit the file /etc/default/pure-ftpd-common
nano /etc/default/pure-ftpd-common
and make sure that the start mode is set to standalone and set VIRTUALCHROOT=true:
STANDALONE_OR_INETD=standalone
VIRTUALCHROOT=true
Save and close
Now we configure PureFTPd to allow FTP and TLS sessions. FTP is a very insecure protocol because all passwords and all data are transferred in clear text. By using TLS, the whole communication can be encrypted, thus making FTP much more secure.
If you want to allow FTP and TLS sessions, run
echo 1 > /etc/pure-ftpd/conf/TLS
In order to use TLS, we must create an SSL certificate. I create it in /etc/ssl/private/, therefore I create that directory first:
mkdir -p /etc/ssl/private/
Afterwards, we can generate the SSL certificate as follows:
openssl req -x509 -nodes -days 7300 -newkey rsa:2048 -keyout /etc/ssl/private/pure-ftpd.pem -out /etc/ssl/private/pure-ftpd.pem
Country Name (2 letter code) [AU]: PK
State or Province Name (full name) [Some-State]: SINDH
Locality Name (eg, city) []: Karachi
Organization Name (eg, company) [Internet Widgits Pty Ltd]: TECHNOCRACY
Organizational Unit Name (eg, section) []: IT
Common Name (eg, YOUR name) []: labserver.example.com
Email Address []: manager@example.com
Change the permissions of the SSL certificate:
chmod 600 /etc/ssl/private/pure-ftpd.pem
Then restart PureFTPd:
service pure-ftpd-mysql restart
Edit /etc/fstab. Mine looks like this (I added ,usrjquota=quota.user,grpjquota=quota.group,jqfmt=vfsv0 to the partition with the mount point /):
nano /etc/fstab
UUID=f539c5cb-624f-4c27-a149-1446a251a453 / ext4 errors=remount-ro,usrjquota=quota.user,grpjquota=quota.group,jqfmt=vfsv0 0 1
UUID=8d3194e7-edb5-4492-937d-d066b4994baf none swap sw 0 0 /dev/sr0 /media/cdrom0 udf,iso9660 user,noauto 0 0
To enable quota, run these commands:
mount -o remount /
quotacheck -avugm
quotaon -avug
Install BIND DNS Server
BIND can be installed as follows:apt-get install bind9 dnsutils
If your server is a virtual machine, then it is highly recommended to install the haveged daemon to get a higher entropy for DNSSEC signing. You can install haveged on nonvirtual servers as well, it should not hurt.
apt-get install haveged
Install Webalizer and AWStats
Webalizer and AWStats can be installed as follows:apt-get install webalizer awstats geoip-database libclass-dbi-mysql-perl libtimedate-perl
Open /etc/cron.d/awstats afterwards
nano /etc/cron.d/awstats
and comment out everything in that file:
#MAILTO=root
#*/10 * * * * www-data [ -x /usr/share/awstats/tools/update.sh ] && /usr/share/awstats/tools/update.sh
# Generate static reports:
#10 03 * * * www-data [ -x /usr/share/awstats/tools/buildstatic.sh ] && /usr/share/awstats/tools/buildstatic.sh
Install Jailkit
Jailkit is needed only if you want to chroot SSH users. It can be installed as follows:apt-get install build-essential autoconf automake libtool flex bison debhelper binutils
cd /tmp
wget http://olivier.sessink.nl/jailkit/jailkit-2.19.tar.gz
tar xvfz jailkit-2.19.tar.gz
cd jailkit-2.19
echo 5 > debian/compat
./debian/rules binary
You can now install the Jailkit .deb package as follows:
cd ..
dpkg -i jailkit_2.19-1_*.deb
rm -rf jailkit-2.19*
Install fail2ban and UFW Firewall
This is optional but recommended, because the ISPConfig monitor tries to show the log:apt-get install fail2ban
To make fail2ban monitor PureFTPd and Dovecot, create the file /etc/fail2ban/jail.local:
nano /etc/fail2ban/jail.local
And add the following configuration to it.
[pure-ftpd]
enabled = true
port = ftp
filter = pure-ftpd
logpath = /var/log/syslog
maxretry = 3
[dovecot]
enabled = true
filter = dovecot
logpath = /var/log/mail.log
maxretry = 5
[postfix-sasl]
enabled = true
port = smtp
filter = postfix-sasl
logpath = /var/log/mail.log
maxretry = 3
Restart fail2ban afterwards:
service fail2ban restart
To install the UFW firewall, run this apt command:
apt-get install ufw
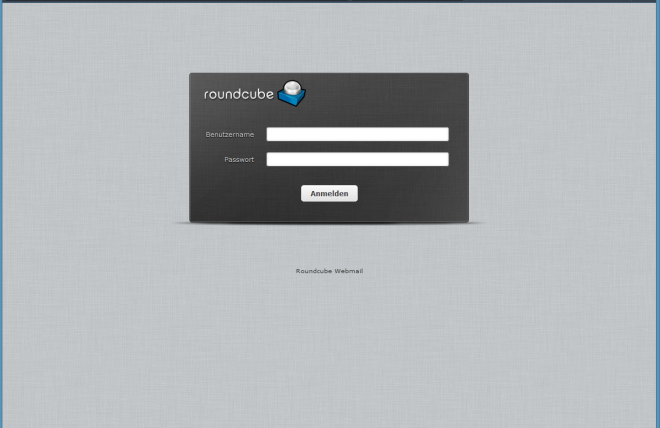
Install RoundCube
Install RoundCube with this command:apt-get install roundcube roundcube-core roundcube-mysql roundcube-plugins
The installer will ask the following questions:
Configure database for roundcube with dbconfig.common? yes
MySQL application password for roundcube: Hit Enter
Password of the databases administrative user: (mysqlrootpassword)
Then edit the RoundCube /etc/roundcube/config.inc.php file and adjust a few settings:
nano /etc/roundcube/config.inc.php
Set the default_host and smtp_server to localhost.
$config['default_host'] = 'localhost';
$config['smtp_server'] = 'localhost';
Then edit the Apache roundcube configuration file /etc/apache2/conf-enabled/roundcube.conf:
nano /etc/apache2/conf-enabled/roundcube.conf
And add an alias line for the apache /webmail alias, you can add the line right at the beginning of the file. NOTE: Do not use /mail as alias or the ispconfig email module will stop working!
Alias /webmail /var/lib/roundcube
Then reload Apache:
service apache2 reload
Now you can access RoundCube as follows:
http://192.168.1.100/webmail
http://www.example.com/webmail
http://labserver.example.com:8080/webmail (after you have installed ISPConfig, see the next chapter)
Install ISPConfig 3
You can install ISPConfig 3 from the latest released version using the following:cd /tmp
wget http://www.ispconfig.org/downloads/ISPConfig-3-stable.tar.gz
tar xfz ISPConfig-3-stable.tar.gz
cd ispconfig3_install/install/
The next step is to run the ISPConfig installer.
php -q install.php
This will start the ISPConfig 3 installer. The installer will configure all services like Postfix, Dovecot, etc.
--------------------------------------------------------------------------------
_____ ___________ _____ __ _ ____
|_ _/ ___| ___ \ / __ \ / _(_) /__ \
| | \ `--.| |_/ / | / \/ ___ _ __ | |_ _ __ _ _/ /
| | `--. \ __/ | | / _ \| '_ \| _| |/ _` | |_ |
_| |_/\__/ / | | \__/\ (_) | | | | | | | (_| | ___\ \
\___/\____/\_| \____/\___/|_| |_|_| |_|\__, | \____/
__/ |
|___/
--------------------------------------------------------------------------------
>> Initial configuration
Operating System: Debian 9.0 (Stretch) or compatible
Following will be a few questions for primary configuration so be careful.
Default values are in [brackets] and can be accepted with
Tap in "quit" (without the quotes) to stop the installer.
Select language (en,de) [en]: Hit Enter
Installation mode (standard,expert) [standard]: Hit Enter
Full qualified hostname (FQDN) of the server, eg server1.domain.tld [server1.canomi.com]: Hit Enter
MySQL server hostname [localhost]: Hit Enter
MySQL server port [3306]: Hit Enter
MySQL root username [root]: Hit Enter
MySQL root password []: Enter your MySQL root password
MySQL database to create [dbispconfig]: Hit Enter
MySQL charset [utf8]: Hit Enter
Configuring Postgrey
Configuring Postfix
Generating a 4096 bit RSA private key
.......................................................................++
........................................................................................................................................++
writing new private key to 'smtpd.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]: PK
State or Province Name (full name) [Some-State]: SINDH
Locality Name (eg, city) []: Karachi
Organization Name (eg, company) [Internet Widgits Pty Ltd]: TECHNOCRACY
Organizational Unit Name (eg, section) []: Hit Enter
Common Name (e.g. server FQDN or YOUR name) []: labserver.example.com
Email Address []: Hit Enter
Configuring Mailman
Configuring Dovecot
Configuring Spamassassin
Configuring Amavisd
Configuring Getmail
Configuring BIND
Configuring Jailkit
Configuring Pureftpd
Configuring Apache
Configuring vlogger
Configuring Metronome XMPP Server
writing new private key to 'localhost.key'
-----
Country Name (2 letter code) [AU]: PK
State or Province Name (full name) [Some-State]: SINDH
Locality Name (eg, city) []: Karachi
Organization Name (eg, company) [Internet Widgits Pty Ltd]: TECHNOCRACY
Organizational Unit Name (eg, section) []: Hit Enter
Common Name (e.g. server FQDN or YOUR name) []: labserver.example.com
Email Address []: Hit Enter
Configuring Ubuntu Firewall
Configuring Fail2ban
[INFO] service OpenVZ not detected
Configuring Apps vhost
Installing ISPConfig
ISPConfig Port [8080]:
Admin password [admin]:
Do you want a secure (SSL) connection to the ISPConfig web interface (y,n) [y]: Hit Enter
Generating RSA private key, 4096 bit long modulus
.......................++
................................................................................................................................++
e is 65537 (0x10001)
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]: PK
State or Province Name (full name) [Some-State]: SINDH
Locality Name (eg, city) []: Karachi
Organization Name (eg, company) [Internet Widgits Pty Ltd]: TECHNOCRACY
Organizational Unit Name (eg, section) []: Hit Enter
Common Name (e.g. server FQDN or YOUR name) []: labserver.example.com
Email Address []: Hit Enter
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []: Hit Enter
An optional company name []: Hit Enter
writing RSA key
Configuring DBServer
Installing ISPConfig crontab
no crontab for root
no crontab for getmail
Detect IP addresses
Restarting services ...
Installation completed.
The installer automatically configures all underlying services, so no manual configuration is needed.
Now you can access ISPConfig 3 under http(s)://labserver.example.com:8080/ or http(s)://192.168.1.100:8080/ ( http or https depends on what you chose during installation). Log in with the username admin and the password admin (you should change the default password after your first login):
